

Your cybersecurity requires stable and proactive cyberdefense solutions. Our experts take on a holistic vision for your cyberdefense, from a user station to critical infrastructure, including an application layer.
From need analysis to finetuning, our advisors rely on our network of top-notch technological partners, to provide you with tailor-made cyber-solutions, in accordance with cybersecurity standards and good practices.
Secure and high-performing networks are crucial for data protection. Your basic tasks may entail security holes, and our Cybersecurity Business Unit offers state-of-the-art solutions to secure your network infrastructure, using the following tools:
• Next-generation firewalls NGFW/NGIPS
• Network Security Policy Management
• Network Access Control
• Network Packet Broker (NPB)
• Network visibility, network traffic behavioral analysis
• Sandboxing
• DNS security
• Server Secure Forwarding Public DNS
• Anti-DDOS Protection
• Network Detection and Response (NDR)
.png)
.png)
.png)
.png)
.png)
.png)
.png)

Your sensitive data should be shielded both with a physical and a software security. Our support in integrating various classification tools, data leak prevention and data encryption, provides an extremely high level of security.
Safeguard efficiently your company’s information assets, thanks to traceability, encryption and data leak prevention solutions.
• Data Leak Prevention
• Data classification and tagging
• Database Activity Monitoring
• Database and file encryption
• HSM (Harware Security Module)
• Hardware Security Module
• PKI Solution


.png)
Reduce the attack surface of your applications and keep them protected against critical risks:
Injections, Authentication systems vulnerabilities, Data exposure, XEE attacks, Broken access control, Incorrect configuration, Cross-Site scripting, etc.
For operational and secure applications, choose built-in security measures
• Application firewall (WAF)
• Application vulnerability scanner (WAS)
• Multi-factor Authentication (MFA)
• Data anonymization





Host and endpoint security cannot be at the expense of user’s productivity and experience.
Ensure prevention, detection and response to attack risks of all your endpoints, with a range of solutions adjusted to each attacker’s modus operandi.
• Filtrage URL (Web Security Gateway)
• Web Security Gateway
• Email Security gateway
• ATM and sale outlet security
• Antivirus solutions
• EDR / XDR protection solutions
• Unified endpoint management solutions (UEM)
• Zero-day detection
• Patch management
• Data encryption
.png)



.png)


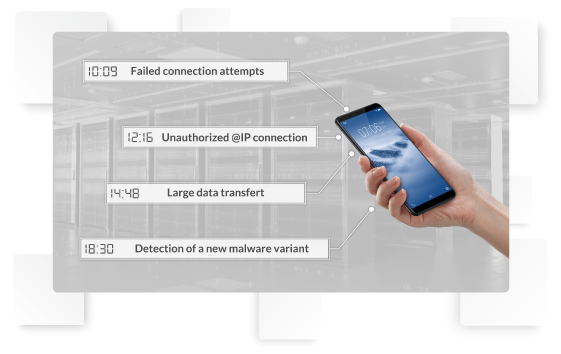
Detect and prioritize threats to minimize their impact with the security intelligence analysis. The security event analysis and real-time detection of malicious behaviors are carried out based on correlation rules, leading to unique alerts (use cases) and a faster incident response.
Thanks to the powerful SIEM solutions, ensure event collection, threat monitoring, accurate detection and analysis, making your infrastructure protection easier.





Besides data storage and protection, you also need data availability, which is a must to guarantee continued services and to show agility when facing cyberattacks.
Take an optimized data management approach via end-to-end solutions:
• Backup management
• Load sharing



Risk-based management of vulnerabilities enables you to improve your asset security.
Our proactive and focused stance builds on:
• Raising user awareness, using our SENSIPRO tool which is designed to meet business needs to involve the teams in all cybersecurity projects
• Vulnerability scanning for a better assessment based on the risk
.png)

Data follow-up is vital to detect security holes. Monitoring tools help you accurately analyze the causes and impacts of attacks, by pointing out the data quality issues
• Privileged access monitoring (PAM)
• Clock synchronization
• File Integrity Monitoring (FIM) (File system – Database – Network Nodes – control lines)
• File Activity Monitoring (FAM)
• Data Activity Monitoring (DAM)






.png)
30+ certified advisors in cybersecurity solutions
200+ Certifications in cybersecurity solutions
Tuning solutions in compliance with Cybersecurity standards and good practices
First-class partnership with leading worldwide Cybersecurity publishers
DATAPROTECT is a cybersecurity company. As a real international key player, DATAPROTECT is strategically positioned in the cybersecurity ecosystem, thanks to its pool of skills and unique expertise.





Copyright 2022